Cum să vezi calea completă a unui folder de rețea mapat
Dacă folosiți foldere de rețea mapate, probabil ca v-ați întâlnit cu situația în care v-a fost trimisă o cale ce conține numele drive-ului mapat, spre exemplu “Z:\Nume Folder”, pe care nu il puteți accesa, primind mesajul că nu găsește calea respectivă.
Pentru a evita aceasta problema, trebuie sa trimiteți calea reală către resursa respectivă, iar pentru a o afla, puteți folosi una dintre metodele enumerate mai jos.
1. Deschideți comand prompt, prin apăsarea combinației de taste Windows key+R, si tastați cmd. Apoi, tastați comanda net use, care vă va afișa calea completă către toate locațiile mapate. Dacă folosiți aceasta metodă, trebuie sa completați manual calea pentru a ajunge la fișierul/folderul dorit.
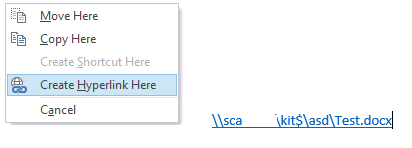
2.Dacă folosiți Microsoft Outlook, deschideți o fereastră pentru crearea unui mail nou, țineți click dreapta apăsat pe share-ul respectiv și trageți către fereastra din Outlook deschisa anterior. Va apărea un meniu, din care selectați opțiunea Create Hyperlink Here. Aceasta metodă vă va afișa cu succes calea completă către fișierul/folderul dorit.
[mai mult...]