Situatie
This guide explains how to disable SSH password authentication for specific user or group in Linux and Unix operating systems. Please note that this will not entirely disable SSH access to users or a group. Instead, it will only disable the SSH password authentication. The users can still access the systems via SSH using other authentication methods, for example key-based authentication.
Solutie
Pasi de urmat
Disable SSH Password Authentication For Specific User Or Group
We can allow or deny SSH access for users and/or a whole group using “/etc/ssh/sshd_config” file in Linux. The sshd_config file has a parameter named “Match” which will help you to disable SSH password authentication for users or groups.
Let us first see how to disable password authentication for a specific user.
Edit “/etc/ssh/sshd_config” file using your favorite editor as root or sudo user:
$ sudo nano /etc/ssh/sshd_config
First, remove the default authentication method by comment out the following line:
#PasswordAuthentication yes
Next, add the following lines at the end:
[...]
Match User senthil
PasswordAuthentication no
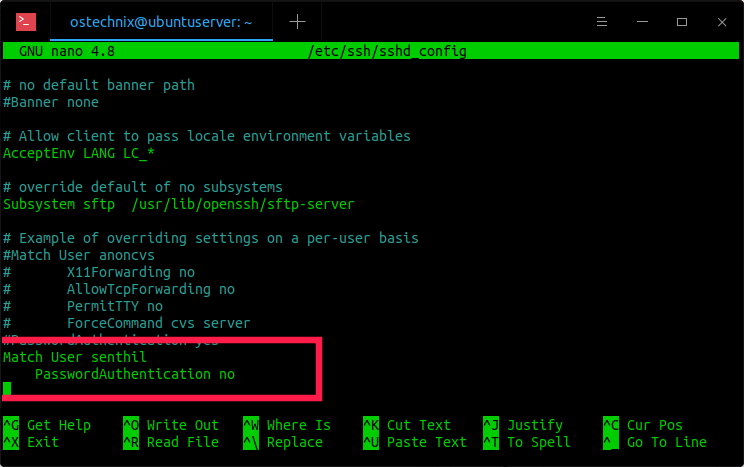
Please note that Match is effective “until either another Match line or the end of the file.” If a keyword appears in multiple Match blocks that are satisfied, only the first instance of the keyword is applied.
As per the above example, we have disabled the SSH password authentication for the user called “senthil”. Replace “senthil” with your own username. Save and close the file. Restart ssh service to take effect the changes:
$ sudo systemctl restart ssh
Now try to login as user “senthil” via SSH:
$ ssh senthil@192.168.225.53
You will see the following error message:
senthil@192.168.225.53: Permission denied (publickey).
Disable SSH password authentication for a group
To disable SSH password authentication for a specific Group, just replace the user name with the group name in the sshd_config file.
Match Group mygroup
PasswordAuthentication no
Replace “mygroup” in the above configuration with your own group name.
Don’t forget to restart the ssh service to apply the changes.
Disable SSH password authentication for multiple users
You can deny SSH password authentication for multiple users by mentioning the user names with comma-separated like below:
Match User senthil,kumar
PasswordAuthentication no
The above example configuration will prevent SSH password authentication for users “senthil” and “kumar”.
Disable SSH password authentication for all users except root user
In some Linux systems, you might want to allow SSH password authentication for “root” user only and disable it for all other users. If so, add the following line in sshd_config file at the end:
Match User !root
PasswordAuthentication no
Restrict SSH password authentication by host or IP address
Not just user or group, we can deny SSH password authentication by host or IP address as well.
For example, the following example will prevent SSH access from a host that contains the IP address:
Match Address 192.168.225.37
PasswordAuthentication no
To limit SSH password authentication for a specific range of IP addresses, add this:
Match Address 192.168.225.*
PasswordAuthentication no
And this example will deny SSH access using password from a host that contains the hostname:
Match Address hostname
PasswordAuthentication no
For more details, refer man pages.
$ man sshd_config

Leave A Comment?