Your iPhone’s Lock Screen has built-in media playback controls that appear whenever music, a podcast, or other audio is playing. What you might not realize is that those controls can also include a volume slider that lets you adjust the volume without you having to unlock your iPhone or fumble for the physical buttons.
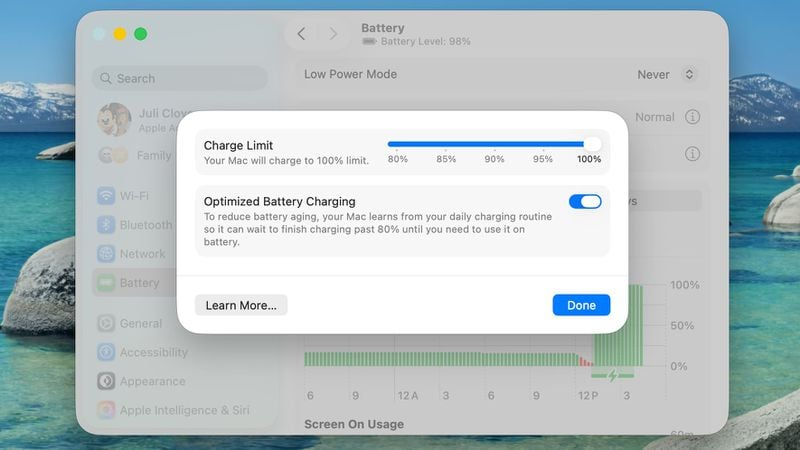
Originally, Apple included a volume slider in the Lock Screen media player by default, but it quietly removed the function in iOS 16. It eventually returned as an option in iOS 18.2, but Apple decided to bury it in Accessibility settings, where it’s easy to overlook. The setting is still available in iOS 26, and it’s super-simple to enable.
Here’s how to turn it on:
[mai mult...]